A common topic I would like to call out which I see in regards to security has to do with endpoints. I kind of want to call those endpoints “potentially vulnerable attack vectors”. I am a bit nervous writing “vulnerable” because the endpoints I mention here are secure, which is why I also called out “potentially”. That’s because you don’t know what you don’t know and maybe there is some unknown or undiscovered exploit. I don’t know of any, but I think a good approach is to expose as few endpoints as possible which reduces the number of potentially vulnerable attack vectors. One of those is the basic authentication endpoint which is exposed via the KUDU/SCM endpoint exposed from both an Azure App Service and an Azure Function. I have no reason to be concerned about using Basic Authentication so long that it’s used in parallel with TLS and a strong cipher. Strongly consider making Multi Factor Authentication (MFA) a mandatory part of your identity strategy as well.
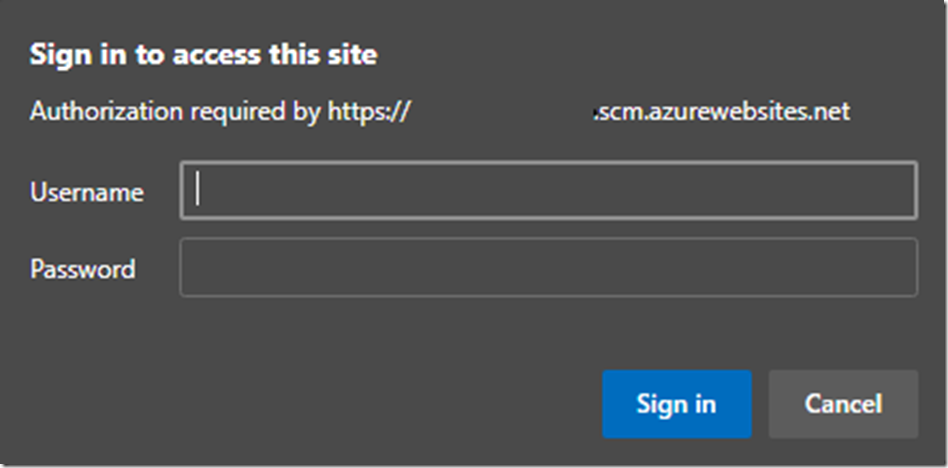
I specifically wrote about using the publish profile credential to access KUDU/SCM using the basic authentication endpoint here, titled “How to access KUDU using your Publishing Profile”. The endpoint is still enabled and can still be used, see Figure 1. Entering in the publishing profile credentials resulted in a successful login, as expected. The point of this article is to explain how to disable that basic authentication endpoint, not because it isn’t secure, but rather to reduce the exposure of an endpoint which might get probed.
Figure 1, basic authentication in Azure App Service
Here is an official document about how to do this, with some additional information of value.
I do it here as well because I have always liked trying these things out for myself.
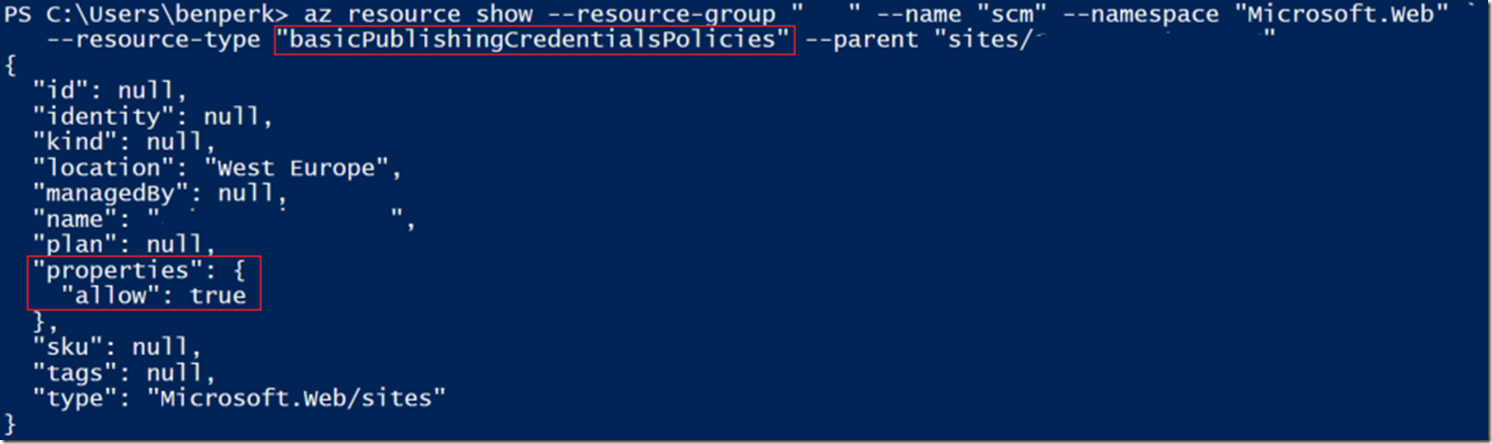
The first action is to take a look at the current setting for the scm resource-type of basicPublishingCredentialsPolicies. To do this you can use Azure CLI as shown here, the results are shown in Figure 2, notice “allow”: true.
az resource show –resource-group “RGNAME” –name “scm” –namespace “Microsoft.Web” `
–resource-type “basicPublishingCredentialsPolicies” –parent “sites/APPNAME”
Figure 2, checking the current value of Basic Authentication KUDU/SCM endpoint
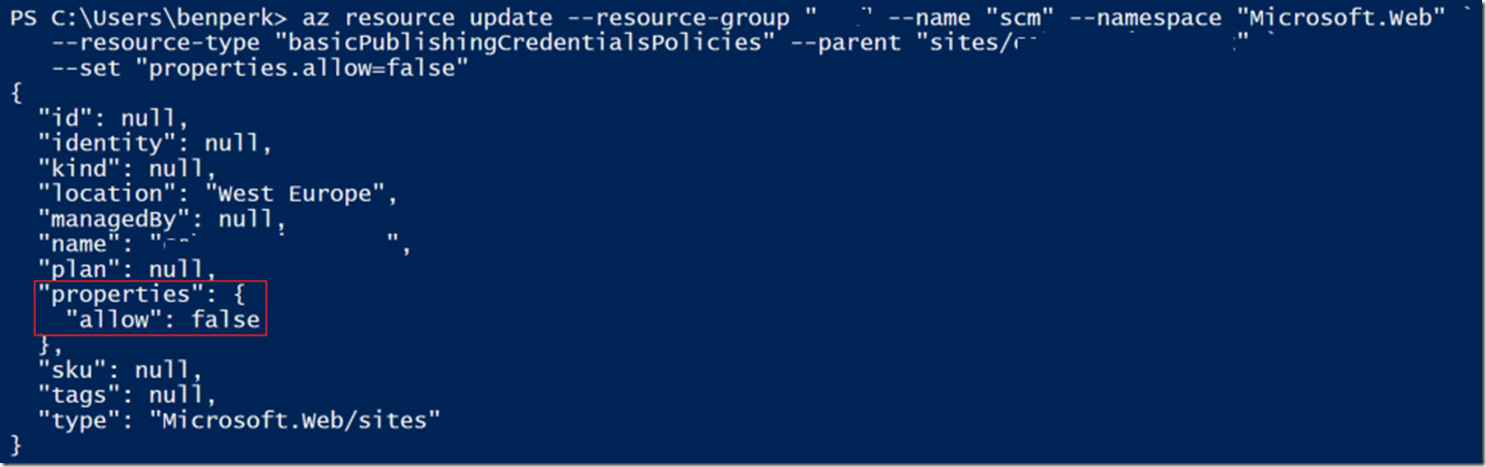
To disable this endpoint, enter the following Azure CLI command, see Figure 3 for the output.
az resource update –resource-group “RGNAME” –name “scm” –namespace “Microsoft.Web” `
–resource-type “basicPublishingCredentialsPolicies” –parent “sites/APPNAME” `
–set “properties.allow=false”
Figure 3, disabling the Basic Authentication endpoint on Azure App Service and Azure Functions
Just to make sure the setting was applied, rerun the az resource show command. And of course, try to login using the endpoint. It should then be disabled and access denied. The endpoint is still discoverable, but I can no longer get access to the KUDU/SCM console using the publishing profile credentials. This is partially ok only. Partially, because the endpoint is still there and my objective was to remove attack vectors. You must consider that the nature of internet / web applications is that they are accessible to the public, friend or foe. If this still gives you some concern you might consider completely stopping the KUDU/SCM for your production slot. Since you shouldn’t be deploying straight into production anyway, you might find this a valid option. Other options you might consider are:
Here are a few useful links about Azure App Service security.
- Security in Azure App Service
- Disabling basic auth on App Service
- Security recommendations for App Service
- Authentication and authorization in Azure App Service and Azure Functions
- Security controls for Azure App Service
- Azure Policy Regulatory Compliance controls for Azure App Service