As you may already know SSL/TLS is offloaded on the Front Ends (*) and this is where certificate root chains are validated (AFAIK). There is no way for you to access those machines to dump out what CAs are there. The next, or closest thing I can think of is to dump them out via the KUDU PowerShell console. I discuss KUDU here.
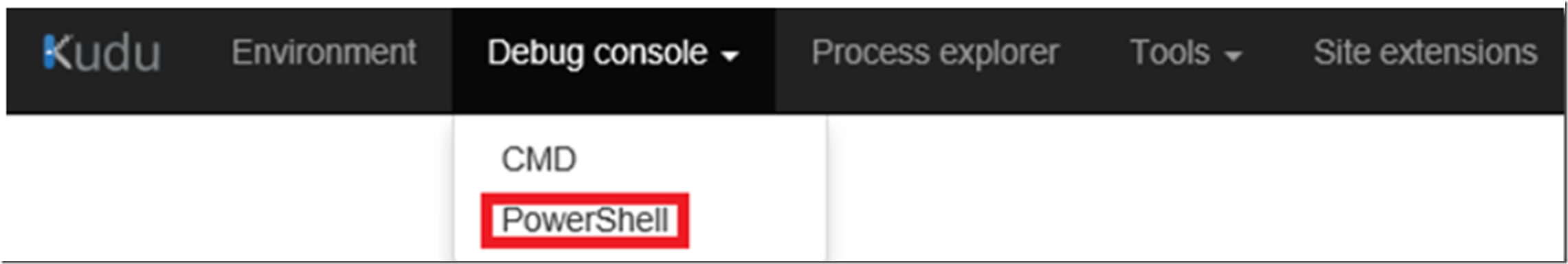
After you login to KUDU, open the PowerShell console, as illustrated in Figure 1.
Figure 1, what CAs exist on Azure App Services
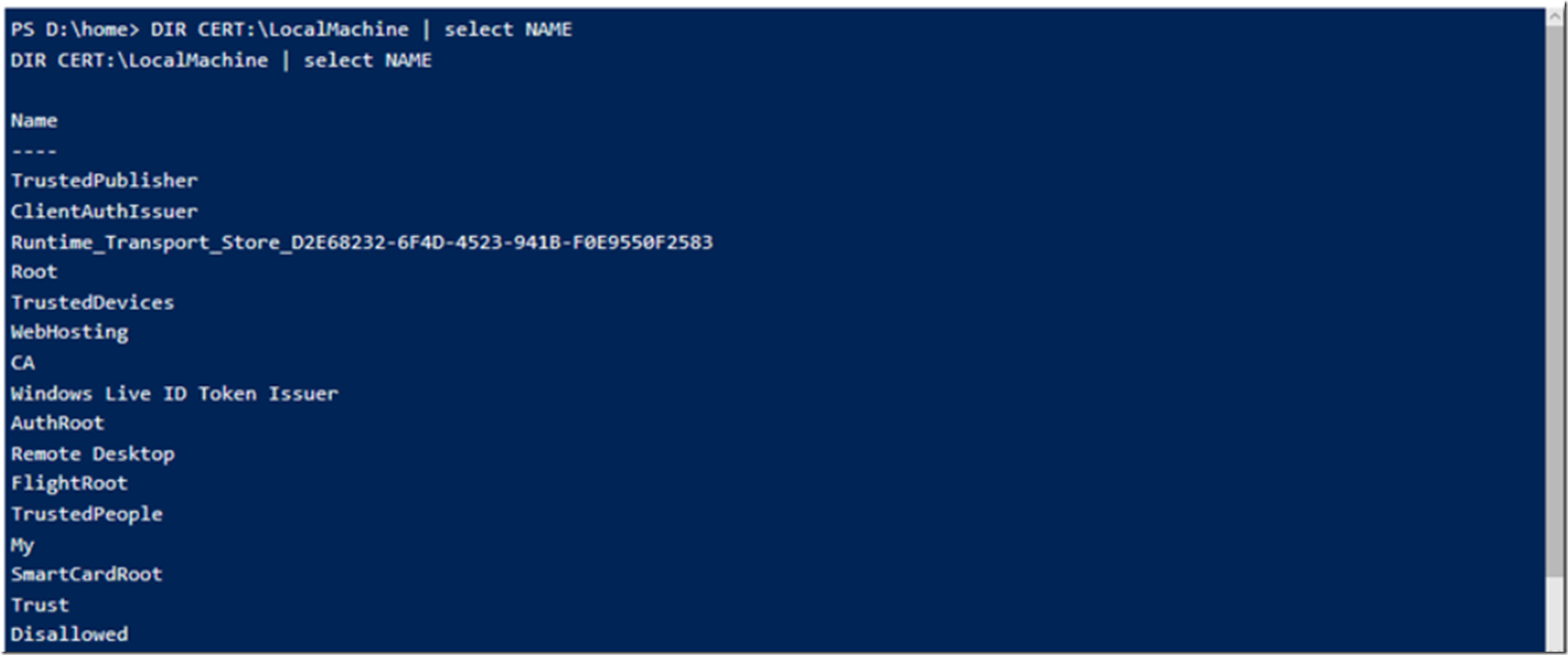
Execute this PowerShell cmdlet which dumps out the Certificate Store Names, see Figure 2.
DIR CERT:\LocalMachine | select NAME
Figure 2, what certificates exist on an Azure App Service
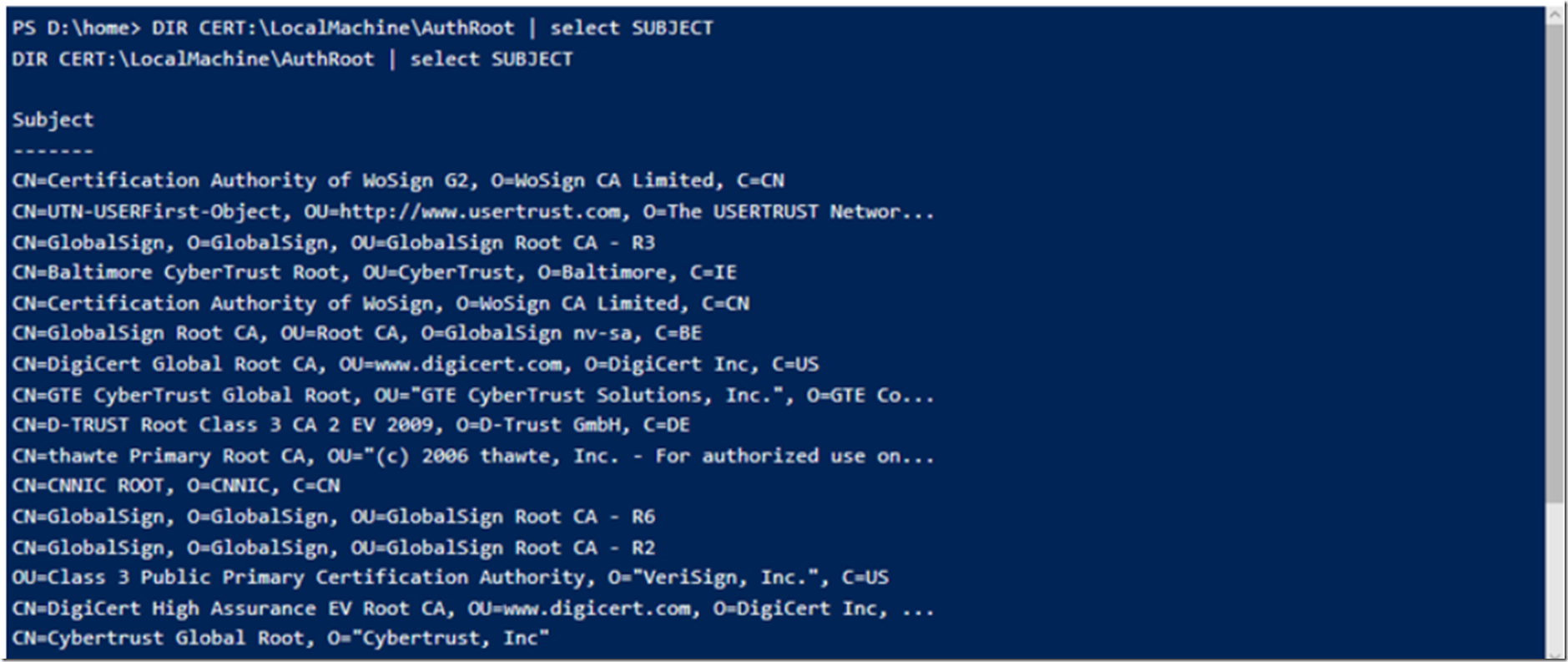
Then if I want to look at the Authorized Root Certificates, I execute this PowerShell cmdlet, see Figure 3.
Figure 3, what Authorized Root Certificates exist on an Azure App Service
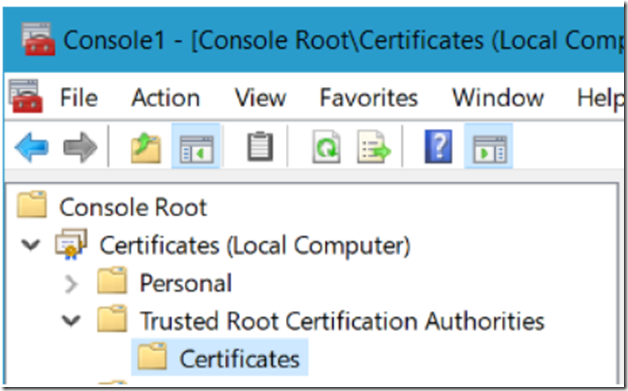
I would expect the output seen in Figure 3 to be the same as if you were to start CERTMGR -> add the Local Computer store and navigate to Trusted Root Certificate Authorities -> Certificates, as seen in Figure 4.
You cannot add Root Certificates to an App Service. You can add intermediate certificates, see here.
Like I mentioned at the beginning, this is what you would see on the App Service machine that is running your application, it is not the place where you would expect to see your SSL/TLS certificate. Those are installed an configured on the Front End, see here.
Also, you can install public certificates on Azure App Service now. See here “App Service Certificates now supports public certificates (.cer)”.
Not that you only have access to store into CurrentUser\My certificate store which can then be retrieved via code on an Azure App Service like the following:
var store = new X509Store(StoreName.My, StoreLocation.CurrentUser);
*NOTE: If you are going to do some work with certificates on the Azure platfom, seriously consider Azure Key Vault. Read about that here and here “Get started with Azure Key Vault certificates”.
Check out some of my other security and certificate related posts:
- How to see the cipher suites on an Azure App Service
- Azure App Service IP Based SSL and SNI Based SSL configuration
- How (I) configured an App Service Certificate for my Azure App Service
- How to disable TLS 1.0 on an Azure App Service Web App
- Make a self-signed SHA256 SSL certificate
- Using TLS 1.2 with WCF
- Make your own SSL Certificate for testing and learning
- Secure channel compatibility support with SSL and TLS
- See all of my Security articles